Your API call returns a 401 despite correct credentials. A background service sends malformed headers invisible to browser DevTools. An HTTP analyzer shows you the raw request and response data-exactly what was sent and what came back-so you can pinpoint the cause in minutes instead of hours.
What Is an HTTP Analyzer?
An HTTP analyzer is a tool that captures HTTP/HTTPS traffic between clients and servers, decoding method, URL, headers, cookies, status codes, timing, and body content into a readable format.
A dedicated HTTP request analyzer captures traffic system-wide: desktop applications, background services, CLI tools, mobile emulators, and localhost connections. This visibility matters when debugging OAuth flows across processes, tracing third-party SDK calls, or verifying what your code actually sends versus what you intended.
How HTTP Analyzers Capture Traffic
HTTP analysis tools use one of three capture methods, each with distinct trade-offs:
| Capture Method | How It Works | Pros | Cons |
|---|---|---|---|
| Proxy-based | Routes traffic through a local proxy server (e.g., Fiddler, Charles) | Easy setup for browsers; can modify traffic | Apps must support proxies; requires certificate installation for HTTPS |
| Network driver | Intercepts traffic at the OS level without acting as proxy | Captures all apps including non-proxy-aware ones; no proxy config needed | Windows-only for most implementations |
| Packet capture | Records raw packets from network interface (e.g., Wireshark) | Protocol-agnostic; captures everything | Cannot decrypt HTTPS without private keys; requires filtering to find HTTP |
Many desktop applications, CLI tools, and background services ignore proxy configuration entirely, making their traffic invisible to proxy-based tools. A network driver approach captures traffic system-wide-including localhost connections that proxy tools often miss.
Key Features of HTTP Request Analysis Tools
Effective HTTP request analysis requires more than raw capture. Professional tools provide:
- SSL/TLS decryption - View encrypted HTTPS traffic in plain text without manually installing certificates in each application
- Real-time filtering - Isolate traffic by domain, method, status code, content type, or application process
- Request/response inspection - View headers, cookies, query parameters, and bodies with syntax highlighting for JSON, XML, HTML
- Timing analysis - Break down DNS lookup, connection, TLS handshake, time to first byte, and transfer time
- Search and grouping - Find specific strings across all captured traffic; group by domain or content type
- Export capabilities - Save sessions for later analysis or share with teammates in formats like JSON, CSV, or HAR
Common HTTP Analysis Use Cases
API Debugging
A POST request arrives as a GET request on the server. A JSON body that gets URL-encoded somewhere in your HTTP stack. HTTP request analysis reveals exactly what your code sends versus what you intended. Compare captured requests against API documentation to spot discrepancies in content types, encoding, or request body structure.
Performance Diagnostics
Slow page loads often stem from a single bottleneck hidden among dozens of requests. Timing charts expose which requests consume the most time - whether due to large payloads, slow DNS resolution, or server processing delays. Sorting by response time or size quickly identifies the culprits.
Authentication Flow Analysis
OAuth flows involve multiple redirects, token exchanges, and cookie handling across several domains. Browser DevTools lose context when redirects cross tabs or involve background requests. A system-wide HTTP analyser captures the complete flow in sequence, showing exactly where tokens appear and how they propagate.
Third-Party Integration Testing
When integrating payment gateways, analytics SDKs, or external APIs, you need visibility into outbound requests. An HTTP analyzer shows what data your application sends to third parties - useful for privacy audits, debugging integration failures, and verifying that sensitive data stays where it belongs.
When Browser DevTools Fall Short
Chrome DevTools and Firefox Network panel handle many debugging tasks, but they have structural limitations:
- Browser-only visibility - Cannot capture traffic from desktop applications, background services, or other processes
- Tab isolation - Each tab shows only its own traffic; cross-tab flows require manual correlation
- No localhost capture for external apps - Traffic to localhost from non-browser applications remains invisible
- Limited modification - Cannot easily replay modified requests or mock server responses
- Session persistence - Clearing the page clears the network log; no built-in session save/restore
A dedicated HTTP request analyzer provides system-wide capture, persistent sessions, and active debugging features that browser tools lack.
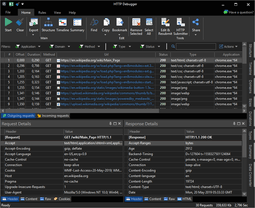
HTTP Analysis with HTTP Debugger
HTTP Debugger takes a different architectural approach than proxy-based tools. It uses a network driver to capture HTTP and HTTPS traffic at the OS level without configuring system proxy settings. This means:
- Traffic from applications that ignore proxy settings gets captured automatically
- Localhost and loopback traffic appears without workarounds
- Applications started before the tool still have their traffic captured
- No certificate installation required for SSL decryption in supported browsers and .NET/Java applications
The interface provides timing charts for request-response analysis, grid-based filtering, JSON/XML tree viewers, and the ability to group and sort captured traffic. Built-in HTTP Submitter lets you modify and resend requests to test different scenarios. Automatic highlighting marks errors, slow requests, and large responses for quick identification.
Frequently Asked Questions
-
Can HTTP analyzers decrypt HTTPS traffic?
Yes. Proxy-based tools require installing a root certificate on the client. Network driver tools like HTTP Debugger can decrypt traffic from browsers and .NET/Java applications without manual certificate installation.
-
What is the difference between Wireshark and an HTTP analyzer?
Wireshark captures all network protocols at the packet level and cannot decrypt HTTPS without private keys. HTTP analyzers focus specifically on HTTP/HTTPS, provide cleaner request-response views, and support SSL decryption.
-
Do I need an HTTP analyzer if I have browser DevTools?
DevTools suffice for browser-originated traffic. You need a dedicated HTTP analyzer for desktop applications, mobile emulators, CLI tools, or authentication flows spanning multiple processes.
-
Can HTTP analyzers modify traffic?
Many include features for modification: editing and resending requests, setting breakpoints, and mocking server responses for testing edge cases and error handling.